When you connect to a VPN, your traffic is encrypted and sent through a “tunnel” to the VPN server. But how is this accomplished? Let’s take a look.
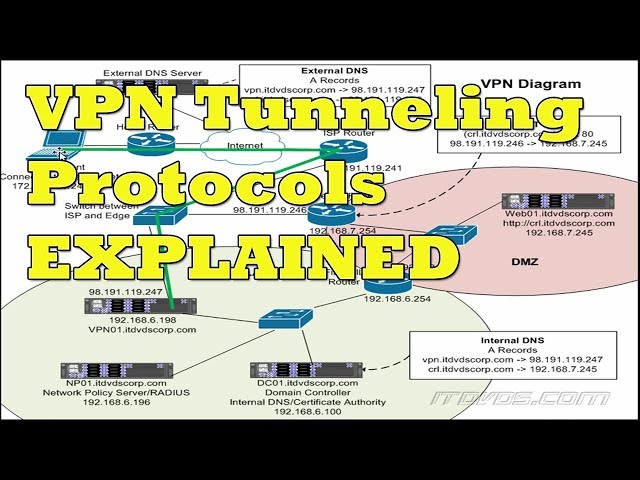 Checkout this video:
Checkout this video:
Introduction
In computer networks, a tunneling protocol is a communications protocol that allows for the secure movement of data from one network to another. A tunnel is created when a tunneling protocol is used to encapsulate data within the original network packet. This creates a “tunnel” between the two networks, allowing for the secure transfer of data.
There are a variety of tunneling protocols in use today, each with its own advantages and disadvantages. The most common tunneling protocols are:
-IPsec: IPsec is a standards-based security protocol that was developed by the IETF. IPsec uses encryption and authentication to protect data in transit. IPsec is often used in VPNs to provide security for data that is being transmitted over an untrusted network.
-L2TP: L2TP is a tunneling protocol that was developed by Cisco and Microsoft. L2TP uses PPP to encapsulate data within an IP datagram. L2TP does not provide any security for data in transit, but can be used in conjunction with IPSec to provide security.
-PPTP: PPTP is a tunneling protocol that was developed by Microsoft. PPTP uses PPP to encapsulate data within an IP datagram. PPTP provides some security for data in transit, but is not as secure as IPSec.
What is a VPN?
Many people use VPNs to protect their privacy online. VPNs encrypt your traffic and route it through a server in another location, making it harder for anyone to snoop on your activity or see your real IP address. But how does this work? Let’s take a closer look.
Types of VPN
A VPN, or Virtual Private Network, creates a secure tunnel between two devices. This tunnel allows for data to be passed through a public or unsecured network in a way that is both private and secure. When you connect to the internet using a VPN, your data is encrypted and your IP address is hidden. This makes it virtually impossible for anyone to track your online activity or steal your personal information.
There are two main types of VPNs: site-to-site and client-to-site.
Site-to-site VPNs are typically used by businesses or organizations that have multiple locations. This type of VPN allows all of the locations to connect to each other securely over the internet.
Client-to-site VPNs are typically used by individuals or businesses with just one location. This type of VPN allows people to connect to a secure network from their individual devices.
Benefits of using a VPN
There are plenty of reasons to use a VPN when you’re online, but the main reason is security. When you connect to the internet without a VPN, your connection is not secure. Anyone on the same network as you can snoop on your traffic and see what you’re doing online.
A VPN encrypts your traffic and route it through a server in another location. This way, no one can snoop on your traffic or see what you’re doing online. A VPN also hides your IP address, making it harder for ISPs and government agencies to track your online activities.
VPNs are also useful for bypassing geo-restrictions. If you want to access content that is only available in another country, you can use a VPN to connect to a server in that country and access the content you want.
There are many other benefits of using a VPN, but these are the main ones. If you’re looking for a secure and private way to browse the internet, a VPN is the best solution.
How is ‘Tunneling’ Accomplished in a VPN?
In computer networks, tunneling is the process of sending data from one network to another. A tunnel is created when data is encapsulated, or wrapped, in a layer of security. This layer is then sent over the network to the destination, where it is decoded and the original data is then sent to the user.
Encapsulation
In order to understand how tunneling works, it is first necessary to understand the concept of encapsulation. Encapsulation is the process of taking data from one protocol and “wrapping” it in another protocol before sending it. For example, when you send an email, your email client will take the text of your message and wrap it in the appropriate headers for the email protocol before sending it off to the server. The same thing happens when you browse the web – your web browser takes the HTML code of the webpage and wraps it in HTTP headers before sending it to the server.
When you tunnel data, you are essentially encapsulating it in another protocol before sending it. This has a few benefits. First, if the data is encrypted, it becomes more difficult for someone who is intercepting the data to read it. Second, if the data is sent over a different protocol than the one that is being used on the network, it can bypass any restrictions that have been placed on that network (for example, if you are tunneling HTTPS traffic over an HTTP connection).
How is ‘Tunneling’ Accomplished in a VPN?
Tunneling is accomplished by encapsulating data in one protocol and then sending it over another protocol. In most cases, this is done by creating a new layer 4 connection – that is, a new connection at the transport layer (layer 4) of the OSI model.
There are two common protocols that are used for tunneling: PPTP and L2TP/IPSec. PPTP is generally faster than L2TP/IPSec but some security experts consider L2TP/IPSec to be more secure.
In order to tunnel data using PPTP, first a PPP connection must be established between the VPN client and server. Once this connection has been established, a GRE (Generic Routing Encapsulation) tunnel can be created between the client and server. GRE is a encapsulation protocol that can be used to send any type of traffic over an IP network – this makes it ideal for use with VPNs.
L2TP/IPSec tunnels work in a similar way to PPTP tunnels but use different protocols at different layers of the OSI model. L2TP (Layer 2 Tunneling Protocol) handles authentication and encryption while IPSec (Internet Protocol Security) handles encryption only.
Both PPTP and L2TP/IPSec tunnels can be configured to use either MPPE (Microsoft Point-to-Point Encryption) or IPSec for encryption. MPPE uses RC4 encryption with 128-bit keys while IPSec uses DES or 3DES encryption with 56-bit or 168-bit keys respectively.
Secure Sockets Layer (SSL)
Secure Sockets Layer (SSL) is the most common type of tunneling protocol used in a VPN. SSL uses a combination of public key and symmetric key encryption to create a secure connection between two devices. When an SSL VPN client software program is installed on a user’s computer, it creates an encrypted tunnel between the user’s computer and the VPN server. Any data that travels through this tunnel is protected from being read or intercepted by anyone who does not have the correct encryption key.
Transport Layer Security (TLS)
Transport Layer Security, or TLS, is a form of tunneling that uses public key encryption to secure data being sent between two machines. TLS is most commonly used in web browsers to protect traffic going to and from websites, but it can also be used to secure other kinds of internet traffic, such as email.
Conclusion
‘Tunneling’ is a word often used in networking. It’s a way of concealing data so that it can be transmitted securely without being intercepted. The most common type of tunneling is done through a Virtual Private Network (or VPN).
A VPN tunnel is created when data is encapsulated, or wrapped, in an outer layer of encryption. This outer layer is called a ‘tunnel’. The data inside the tunnel is then transmitted to its destination. When the data reaches its destination, the tunnel is opened and the data is decrypted and sent on its way.
Using a VPN tunnel has several advantages. First, it allows you to transmit data securely over public networks such as the Internet. Second, it can help you bypass firewalls and other restrictions that may be in place on your network. Finally, it can give you a way to connect to remote networks securely.
If you’re thinking about using a VPN, be sure to choose a reputable provider with strong security features. And make sure that the tunneling protocol they use is compatible with your devices and operating system.
